Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.

Critical Vulnerabilities Discovered in Automated Tank Gauge Systems
Bitsight TRACE explores several critical vulnerabilities discovered in ATG systems and their inherent risk when exposed to the Internet.

Discover the complexities of exposure management in the cybersecurity landscape, as we dissect the acronyms and delve into the fundamental need for better visibility into asset states.

We’re back again with a monthly-ish blog reflecting on major goings on in the security world.

While all areas of risk management involve blind spots, supply chain risk management might be the murkiest. To be effective in this field, risk professionals must account for risks from a wide variety of sources, from bad password management to geopolitical upheaval. Supply chain risks can be difficult to detect, unpredictable, and fast-moving.

Explore the concerning cybersecurity landscape in Australia's finance sector, marked by major data breaches and deficiencies in notification procedures, highlighting critical vulnerabilities and pressing challenges.

What is adaptive security? Explore the benefits of this approach to cyber risk reduction and how your organization can get started.

Key risk indicators (KRIs) can help monitor and control cyber risk. But what KRIs should you focus on?

Tim Grieveson from Bitsight discusses strategies for managing Shadow IT, emphasizing the need for cybersecurity leaders to balance security and convenience.

A monthly or quarterly report is a great way to summarize a SOC’s performance and uncover insights for executive leadership. But as a security and risk manager or executive, what information should you request from the managers who report to you?
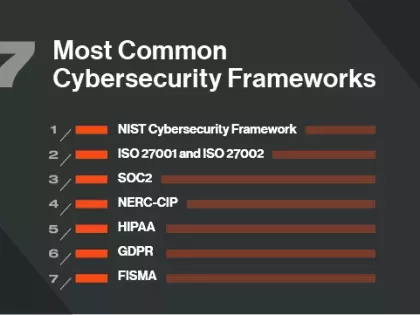
While security ratings are a great way to demonstrate that you’re paying attention to the cyber health of the organization you also need to show that you’re adhering to industry and regulatory best practices for IT security and making informed decisions for the long-term. A cybersecurity framework can help.

Read the latest Bitsight research on PrivateLoader including important updates recently, including a new string encryption algorithm, a new alternative communication protocol and more.
Is there a difference between cybersecurity vs. information security? Learn more about the distinctions between the two areas, where they overlap, and how both have evolved.

Failing to update your software doesn’t just mean you’re missing out on the latest version—it means you could expose your organization to major security vulnerabilities, like the widespread Apache Log4j2 vulnerability.

Anders Norremo from Bitsight unveils key insights into simplifying your approach to Third Party Risk Management (TPRM). By integrating solutions like Bitsight's Vendor Risk Management, you can streamline vendor assessments, enhance efficiency and automate processes.

Open port vulnerabilities can increase cyber risk exposure. Learn what they are and how you can quickly find and fix them.

Is cybersecurity risk defined in the same way as common risk? How is it different? Find out the answers and what you can do about it.