The Challenge
As a financial company with over $17.5B in total assets it is important to not only have clarity into its cyber security risk landscape, but also to perform effective cost-based decision making to justify investments and budgets, including:

- Clearly quantifying the top cyber risks, identifying areas of high-risk exposure, then evaluating various applicable risk mitigation strategies, taking into consideration which risk scenarios the risk mitigation(s) will impact and how.
- Either reducing the probability of that risk event and/or reducing the financial impact of the risk event if it were to occur.
In this case study, this company identified a high degree of risk exposure tied to a malicious actor possibly gaining access to their shared storage, affecting the confidentiality of sensitive data.
Post author Christina Dulovich is a RiskLens Senior Risk Consultant
Management needed to know what control(s) to put into place to halt external actors from exfiltrating sensitive information: data purge, role-based access segmentation or drive encryption?
The organization’s conventional approach to risk rankings could not support executive management’s decision directly. The organization turned to the RiskLens platform to understand the risk in terms best understood by business stakeholders: return on investment (ROI).
The Solution
The RiskLens platform features an intuitive workflow process for:
- Scoping risk scenarios (with the option to choose among pre-packaged, common scenarios)
- Collecting data from within the organization, as well as industry data curated by RiskLens. Handy Data Helpers and Loss Tables store the data for repeat, easy access.
- Estimating current probable loss exposure with a sophisticated analytics engine based on Factor Analysis of Information Risk (FAIR™), the industry standard for the quantification of information security risk.
- Running cost benefit analysis, for a view on probable risk reduction in dollars from controls options
The analyst team began by focussing on the amount of risk associated with an external actor breaching sensitive information held on their workstation shared storage, putting the data at risk of exfiltration
They used the simple scoping capability within RiskLens to rapidly determine what data points were necessary for the analysis. Analysts then collected data through the guided workshop questions on the platform, covering key risk and control factors including:
- Historical instances of an external actor attempting to gain unauthorized access to their shared storage via compromised credentials
- Existence of monitoring tools
- Segmentation of the data
- Likely number of sensitive records held in their shared storage locations
- Resources required to respond to the breach
- Fines imposed from applicable regulations or court judgments
Figure 1
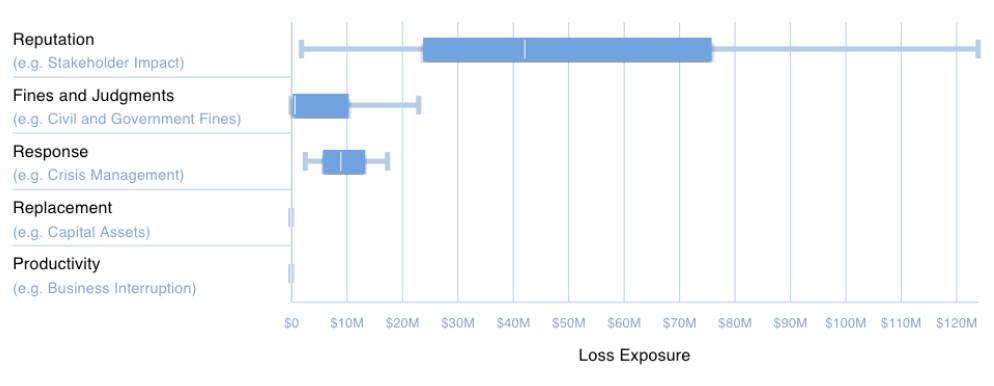
Based on the collected data, the team ran an analysis using the Monte Carlo functionality of the platform to establish the current state of risk as loss exposure in dollars. Figure 1 illustrates the ranges of probable loss exposure across several categories that incorporate incident response efforts, regulatory fines, and response efforts to those affected by the breach and reputation (loss of customers).
The comparison capability of RiskLens also allows future state, “what-if” analyses to be rapidly performed. In this scenario, analysts leveraged the tool’s comparison capability to model and compare the risk exposure reduction from performing a data purge, implementing drive encryption, or further enhancing their role-based access to their drives.
Additionally, they captured the investment cost needed for each of the three potential future states, to identify the return on investment (ROI). These comparison reports provided the organization with tangible data to decide on the type of control to implement. The results were telling – one type of investment clearly outweighed the others in terms of risk reduction.
Key Benefits
The RiskLens platform allowed the organization to rapidly quantify the loss exposure of an external actor accessing shared storage via compromised credentials. Additionally, the quantitative inputs a documented rationale provided an opportunity for stakeholders to review and challenge the inputs used during the analysis. More importantly, it equipped management with data to make a strategic decision on the type of control to invest in while maximizing their risk reduction.
|
Risk Reduction Driver of Data Purge Decrease in impact of the loss event via less exposed records |
|---|
|
Risk Reduction Driver of Drive Encryption Decrease in impact of the loss event via sensitive information exposed not being plain text |
|
Risk Reduction Driver of Role-Based Access Decrease in impact of the loss event via less records accessed and exposed via compromised credential |
Figure 2

Figure 2 compares the loss exposure for the current state environment compared to the loss exposure if each of the three controls were implemented. Current state loss exposure (average) was $6M annualized.
Implementing drive level encryption had the largest risk reduction impact, $5.8M, driven by the reduction of external costs associated with the data exposure, as the data being exposed is encrypted and not plain text, resulting is drastically different levels of fines and judgements, notification requirements, and potential reputation damage from this loss event.
This control implementation had an investment cost of roughly $1M. Demonstrating a $5.80 return for every dollar spent in this investment, clearly justifying the effort to implement this control, and supporting the budget necessary. Using the RiskLens platform, for the first time, the analyst team could report results to executive management that were actionable, using the financial terms all stakeholders could understand.